Anthropic flipped the switch on April 30. Claude Security is now in public beta, and every Claude Enterprise customer can start scanning their code today. No procurement cycle. No custom agent build. Just open the sidebar and run a scan.
Two months ago this product was sitting in a quiet research preview with a few hundred companies kicking the tires. Today it ships to every Enterprise tenant. That is a fast turn for a security release.
Table of Contents
- Why this release lands at the right moment
- How Claude Security actually works
- What changed during the preview phase
- Partner ecosystem and platform reach
- Getting started and what to watch for
Why this release lands at the right moment
Cybersecurity timelines are collapsing. The window between vulnerability discovery and weaponized exploitation used to be measured in months. Sometimes weeks. AI is closing that gap fast.
Anthropic put the case plainly in the announcement: working exploits are about to get a lot easier to find, and the next generation of models will be capable of autonomous exploitation. Defenders need frontier capability before the offensive side gets there first.
That is the whole bet behind Claude Security. Put Opus 4.7, currently one of the strongest publicly available models for finding and patching software bugs, in front of every enterprise team that already pays for Claude.
How Claude Security actually works
You can hit it from the Claude.ai sidebar or go straight to claude.ai/security. Pick a repository. Scope it down to a directory or a specific branch if you want. Start the scan.
Then the model does something different from a normal scanner. It does not just grep for known vulnerable patterns or run a CVE signature check. It reads the source. It traces data flow across files and modules. It reasons about how components actually interact in your codebase.
When the scan finishes you get findings with confidence scores attached. Each one comes with severity, likely impact, reproduction instructions, and a proposed patch. You can pop the patch open in Claude Code on the Web and work through the fix in context.
That is the pitch. Read code the way a senior security researcher reads it, then write the fix.
What changed during the preview phase
The research preview ran for roughly two months. Hundreds of organizations of every size pushed the product hard, and three things kept coming back in the feedback.
Detection quality beats raw volume
Teams do not want a thousand findings. They want findings worth acting on. Claude Security runs every result through a multi-stage validation pipeline before an analyst ever sees it. False positives get killed at the source, and every surviving finding gets a confidence rating.
Time from scan to patch is the metric that matters
Several teams in the preview went from running a scan to merging the fix in a single sitting. Not three days of tickets ricocheting between security and engineering. One sitting.
Continuous coverage beats one-off audits
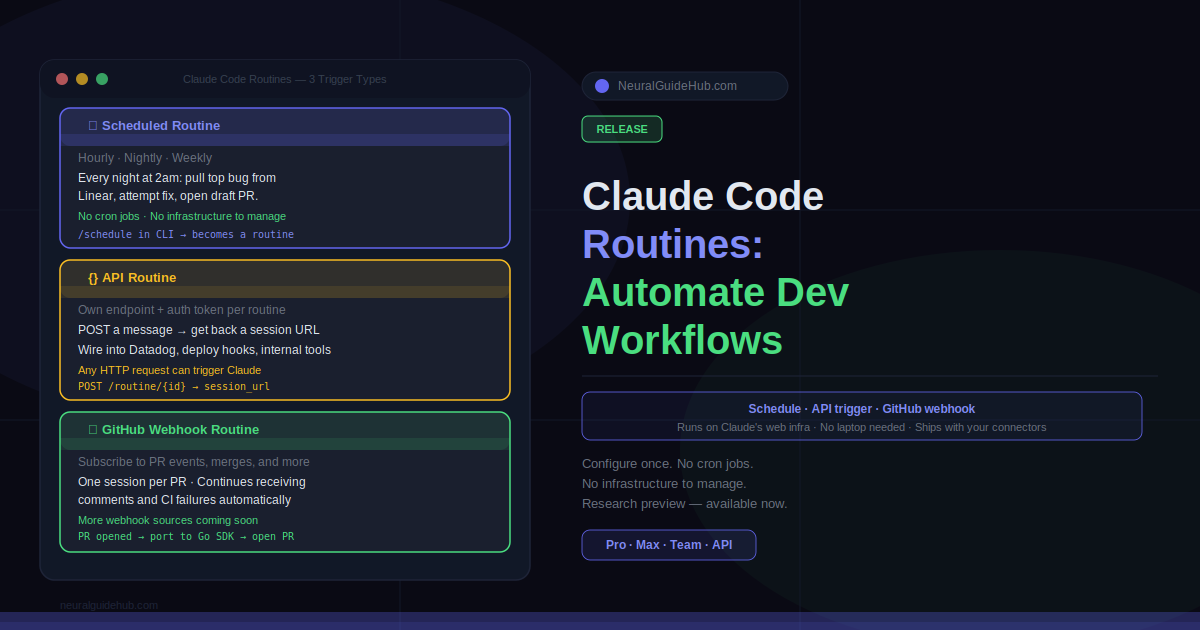
The public beta now includes scheduled scans, so teams can lock in a real cadence instead of treating security review as a quarterly fire drill.
Smaller upgrades stack up too. You can target a scan at a single directory inside a large monorepo. You can dismiss findings with documented reasons so the next reviewer trusts the triage history. You can export results to CSV or Markdown for audit systems, or pipe them into Slack, Jira, or anything else that accepts a webhook.
Partner ecosystem and platform reach
Direct access through Claude Security is one path. The other path is Opus 4.7 already showing up inside the security tools that big enterprises run today.
Anthropic confirmed integrations with CrowdStrike, Microsoft Security, Palo Alto Networks, SentinelOne, TrendAI, and Wiz. On the services side, Accenture, BCG, Deloitte, Infosys, and PwC are standing up Claude integrated programs across vulnerability management, secure code review, and incident response.
The picture is consistent. Whichever way an enterprise already buys security, Opus 4.7 is showing up there.
Getting started and what to watch for
Public beta opened April 30 for Claude Enterprise. Access for Team and Max customers is on the roadmap but not live yet. Admins flip the switch from the admin console, and Anthropic has published a Getting Started guide for the full walkthrough.
One detail worth flagging for security professionals. Opus 4.7 ships with new automatic safeguards that block requests resembling prohibited cyber use. Legitimate defensive teams whose work might trip those filters can join the Cyber Verification Program to keep operating without friction.
The honest take
Most “AI for security” launches in the last two years felt like rebadged static analysis with a chat interface bolted on. This release is different in a specific, narrow way. The reasoning quality is high enough that scan-to-fix actually compresses inside a single afternoon, and that is the only metric that has ever mattered for a vulnerability program.
Whether the quality holds up across messier real-world codebases at full enterprise scale is the open question. The next six months of public beta will answer it. For now, if your organization runs Claude Enterprise, there is no real reason not to point this thing at a repo this week and see what it surfaces.